Tech giants, most of which are from the US, are permeating every aspect of our digital lives from the browser (Chrome), search engine (Google, Bing), and messaging apps (WhatsApp, Messenger) we use, to where we store our private documents (Dropbox, Google Drive, OneDrive) and email messages (Gmail, Outlook).
The Internet was originally conceived as a decentralized, fault-tolerant network of systems, so the increasing dominance of services hosted by only several major tech companies conflicts with the founding principles of the Internet itself.
Privacy-conscious users are increasingly concerned that their personal data from “free” services can be data-mined and sold to third-parties for marketing and behaviorial targeting purposes. Terms of Service, even for paid services such as G Suite or Office 365, are difficult for the average user to understand, and give wide latitude for Google or Microsoft to process your data however they wish.
In a post Cambridge Analytica world, where Facebook was fined $5 billion by the US Federal Trade Commission for lying about retaining personal information that had been scraped from users’ friends lists, it’s increasingly difficult for users to blindly trust that tech giants will even follow their own privacy policies.
The promulgation of information and misinformation has never been so powerful, shaping opinions not only through traditional media such as TV, radio, and newspapers, but every time we scroll through a social media feed. The deliberate manipulation of elections and referendums using psychological models without our consent, translate “fake news” and hateful “dog whistles” into actual political power.
Here’s a checklist that you can follow to replace proprietary services with privacy-respecting, open source applications – to take back control of your digital life.
Switch from Chrome to Firefox
 Google Chrome enjoys a dominant market share, accounting for 68.60% of global browser usage in July 2019 (NetMarketShare). Firefox, which was previously the #1 browser after the second browser wars in the early 2000s, has fallen to 8.34% in market share.
Google Chrome enjoys a dominant market share, accounting for 68.60% of global browser usage in July 2019 (NetMarketShare). Firefox, which was previously the #1 browser after the second browser wars in the early 2000s, has fallen to 8.34% in market share.
Although the Chromium engine which Chrome is built upon is an open source project, the browser itself is a proprietary Google product. By contrast, Firefox is 100% free and open source and maintained by Mozilla, a not-for-profit corporation “for the public good.”
Clearly, it’s in Google’s interest to use the data collected from Chrome browser users to tailor advertising better on its AdWords and DoubleClick platforms – where the search giant derives 83 percent of its total revenue. Although Mozilla does receive some payments to ship Firefox with Google as the default search engine, it doesn’t send telemetry data back to Google. You can turn off Firefox Telemetry so no usage data or crash reports go back to Mozilla.
Chrome plans to restrict ad blocking extensions from blocking ads before they are loaded and limiting the number of rules that an ad blocking extension can use to 30,000, a decision that was clearly made to protect Google’s advertising business.
Firefox doesn’t have these restrictions on ad blockers, since they’re not directly dependent on advertising for revenue.
Use Firefox Containers for Google, Microsoft, Yahoo, Facebook, and Twitter
Firefox Multi-Account Containers and Facebook Container are official add-ons for Firefox that limit the impact of trackers and beacons across the Internet. Advertising networks, such as Facebook’s Audience Network, tracks your browsing habits on any web page with an embedded “Like” or “Share” button, by identifying you based on your Facebook user cookie – even if logged out. In fact, these social sharing widgets can be a major GDPR liability.
Other ad networks owned by Google, Microsoft, Yahoo, and Twitter use similar methods to target advertising based on the interests and persona (gender, age, political beliefs, life events, etc.) that they infer from your browsing history.
In the past, the ways to avoid being tracked such as disabling cookies or using separate browser profiles were rather inconvenient. With Firefox Containers, you can designate certain URLs (e.g. facebook.com, gmail.com, etc.) to be loaded in its own “container” with a separate cookie store. It effectively defeats ad networks’ efforts to track you outside of their properties.
Switch from Chrome to Firefox Mobile
 For the same reasons why you should switch from Chrome to Firefox on the desktop, using Firefox Mobile on your Android or iOS device also bolsters your privacy. In fact, ad blocking add-ons such as uBlock Origin are also available for Firefox Mobile, speeding up your browsing experience and saving mobile data. But there’s a more important reason related to DNS-over-HTTPS, which we’ll cover later in the checklist, why you should consider using Firefox Mobile instead of Chrome (or Mobile Safari).
For the same reasons why you should switch from Chrome to Firefox on the desktop, using Firefox Mobile on your Android or iOS device also bolsters your privacy. In fact, ad blocking add-ons such as uBlock Origin are also available for Firefox Mobile, speeding up your browsing experience and saving mobile data. But there’s a more important reason related to DNS-over-HTTPS, which we’ll cover later in the checklist, why you should consider using Firefox Mobile instead of Chrome (or Mobile Safari).
While performance was not the strong point of older versions of Firefox Mobile, the Kraken JavaScript Benchmark shows that Firefox Mobile’s rendering and scripting performance (4520.2ms) is competitive with Chrome Mobile (5129.3ms) on Android – lower is better. Mozilla has made substancial strides in improving the performance of Firefox Mobile with optimizations to the Gecko rendering engine – with additional improvements on the way in Gecko Quantum.
Use Signal instead of WhatsApp / FB Messenger for OTT Messaging
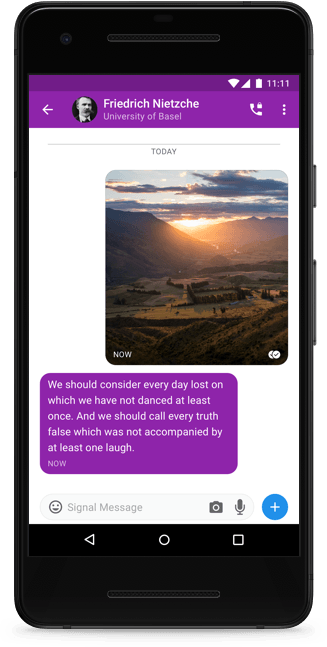 Signal Private Messenger by Open Whisper Systems, is an open-source implementation of the Signal protocol used for end-to-end (E2E) encryption for over-the-top messaging apps. Although Facebook licensed the Signal protocol for WhatApp’s chat encryption capability, there’s no way to know if they’ve built in any backdoors into their implementation because unlike Signal, WhatsApp is a closed-source, proprietary app.
Signal Private Messenger by Open Whisper Systems, is an open-source implementation of the Signal protocol used for end-to-end (E2E) encryption for over-the-top messaging apps. Although Facebook licensed the Signal protocol for WhatApp’s chat encryption capability, there’s no way to know if they’ve built in any backdoors into their implementation because unlike Signal, WhatsApp is a closed-source, proprietary app.
If you use WhatsApp’s backup-and-restore feature with Google Drive, you’re already allowing Facebook to read your chats because they hold the decryption key to your chat and media archives. On the other hand, Signal only backs up your encrypted messages to local phone storage – meaning they have zero-knowledge of the decryption key.
With Signal, the only centralized features of the app are contact discovery and voice/video call routing. As long as you don’t enable the “Always relay calls” option in Signal settings, your encrypted calls are not routed through Signal’s servers – only to establish the call itself.
Facebook Messenger completely lives on Facebook’s infrastructure, even though they claim to offer E2E encryption – they have been under pressure by US law enforcement to install a backdoor that would compromise their users’ privacy. For the same reason, Signal is better than Telegram, because Telegram is also a closed-source app.
Search with DuckDuckGo or StartPage.com instead of Google
 By default, Google and Bing keep a record of your search queries indefinitely, if you use Chrome or Edge, and/or are signed into your Google or Microsoft account. Even if you don’t sign in, Google heavily personalizes your results based on cookie tracking, location (based on your IP address or GPS), and what search results you have previously visited.
By default, Google and Bing keep a record of your search queries indefinitely, if you use Chrome or Edge, and/or are signed into your Google or Microsoft account. Even if you don’t sign in, Google heavily personalizes your results based on cookie tracking, location (based on your IP address or GPS), and what search results you have previously visited.
For this reason, SEO professionals frequently use Incognito (Private Browsing) mode, or even VPNs to change their location – and see unbiased search results to know where they really stand in the search rankings.
Your search and web history are considered by Google and Bing to serve you ads, based not only on contextual targeting (based on each individual search query) but behavioral targeting (what webpages you visit, and previous search patterns).
DuckDuckGo, based in the US, and StartPage.com, based in the Netherlands (EU jurisdiction), are private search engines that have a different approach to advertising. They rely on contextual targeting only, not behavior targeting. Although it means you might see “less relevant” ads, it also means your search results are not biased by your previous searches – In theory, every user in a given country, should see the same set of results on DuckDuckGo or StartPage.com at any given time.
Because crawling the Internet is such a huge undertaking, both DuckDuckGo and StartPage.com are metasearch engines that rely on results licensed from the major search companies. DuckDuckGo uses a combination of Bing, Yahoo, and Yandex results, while StartPage.com exclusively uses Google results.
However because you don’t do the search on Google or Bing directly, your IP address is never revealed to the actual search engine that provided the results – they are proxied by DuckDuckGo or StartPage.com.
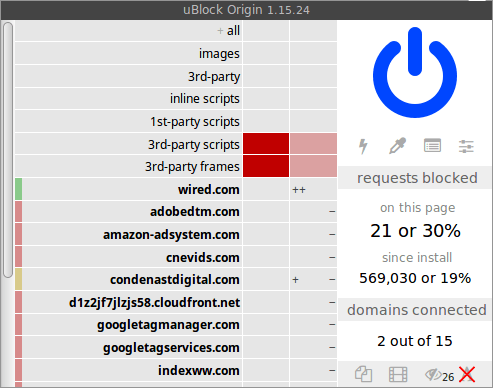
Install an ad blocker such as uBlock Origin
 Not all ad blockers are created equal. Shockingly enough, some ad blocking extensions such as AdBlock, AdBlock Plus, and Ghostery have been caught “red-handed” colluding with the ad networks to whitelist “less intrusive” ads. Large sums of money changes hands to persuade the developers to let certain ads through and not others.
Not all ad blockers are created equal. Shockingly enough, some ad blocking extensions such as AdBlock, AdBlock Plus, and Ghostery have been caught “red-handed” colluding with the ad networks to whitelist “less intrusive” ads. Large sums of money changes hands to persuade the developers to let certain ads through and not others.
uBlock Origin is an open-source ad blocker that uses community-maintained lists to block banner ads, affiliate links, trackers, and browser beacons. Choosing a trustworthy ad blocker is very important, as the add-on has the permissions to modify the content & layout of the webpages you see. An unscrupulous add-on could easily inject malware or phishing links onto any website, and you would be none the wiser (i.e. the padlock symbol would appear with the correct domain in the address bar).
uBlock Origin doesn’t accept donations from the advertising industry for whitelisting, making it our recommendation for an ad blocking plugin that’s compatible not only with Firefox and Firefox Mobile, but also Chrome and Edge Insider (based on WebKit).
Disable Third-Party Trackers and Enable “Do Not Track”
Most websites don’t require third-party cookies to function correctly, unlike same-origin cookies such as session and persistent cookies that are used to login to a website, and remember your username. The vast majority of third-party cookies are used for analytics or advertising purposes, meaning that you won’t experience any loss in functionality by disabling them. Even better, Firefox lets you choose to block third-party cookies that are specifically known as “Third-Party Trackers.”
“Do Not Track” (DNT) is an industry standard that some ad networks and websites comply with as a universal opt-out from tracking. Turning on “Do Not Track” in your browser will automatically indicate the DNT preference to any compliant domains – a DNT compliant domain should act as if nothing is remembered about you, and remember nothing about you.
Except in the jurisdictions that have adopted DNT as a legal standard, complying with DNT is voluntary – so it’s important to disable third-party trackers in conjunction with enabling “Do Not Track” to limit your exposure to tracking cookies.
Enable DNS-over-HTTPS on Firefox
If you thought the padlock symbol and “https://” prefix in your address bar protects your browsing habits from being observed by your ISP or local network, think again. As long as your DNS queries use your ISP’s default DNS servers, it’s trivial for your Internet provider to gather statistics about what domains you visited (and aggregate and sell this data to marketers). Some insidious ISPs have even hijacked mistyped or unreachable domains with their own advertising pages – to squeeze extra revenue out of their subscribers.
Using an alternate DNS server such as CloudFlare DNS, Google Public DNS, OpenDNS, Quad9 is somewhat better because you no longer send your DNS queries directly to your ISP, but still insecure. By default, DNS on port 53 is an insecure protocol that transmits the lookups in plain text, which makes them vulnerable to interception by your ISP (or drag-net surveillance by your country’s intelligence services).
Encrypting your DNS by switching to DNS-over-HTTPS is the best way to mask your DNS traffic from would-be snoopers. CloudFlare DNS is our recommendation, for a few reasons. a) CloudFlare DNS purges all debug logs after 24 hours, and retains KPMG as an auditor of its privacy practices b) they are the leader in implementing new features such as DNS over HTTPS, DNSSEC, TLS 1.3, and Encrypted SNI c) They made an agreement with Mozilla to retain even less data than their standard privacy policy, for Firefox users.
For now, Firefox is the only major browser that supports all of the above features.
Navigate to about:config and make the following changes. Then restart the browser and run the test at EncryptedSNI.com operated by CloudFlare to confirm you pass all 4 tests.
network.trr.mode = 2
network.trr.uri = https://mozilla.cloudflare-dns.com/dns-query
network.trr.bootstrapAddress = 1.1.1.1
network.security.esni.enabled = true
The latter two features, TLS 1.3 and Encrypted SNI also require connecting to a web server that supports those features, such as those running a sufficiently new version of Nginx or Apache, or behind CloudFlare’s CDN. Even if you switch to CloudFlare’s 1.1.1.1 DNS server, you should know that most websites have not yet implemented TLS 1.3 or Encrypted SNI, meaning that the server certificate is not encrypted in the initial handshake, and the domain can be revealed through SNI (a feature used to host multiple HTTPS websites behind a shared IP address).
If you are a activist, journalist, or other sensitive individual who could be in peril if your browsing habits are discovered by your adversaries, you should take additional steps (such as using a correctly configured VPN) to encrypt your entire session, never simply rely on DNS encryption.
Enable DNS-over-HTTPS on Firefox Mobile
Firefox Mobile and Firefox on the desktop practically have the same internals, so the same values (as above) should be changed in about:config to enable DNS-over-HTTPS and Encrypted SNI.
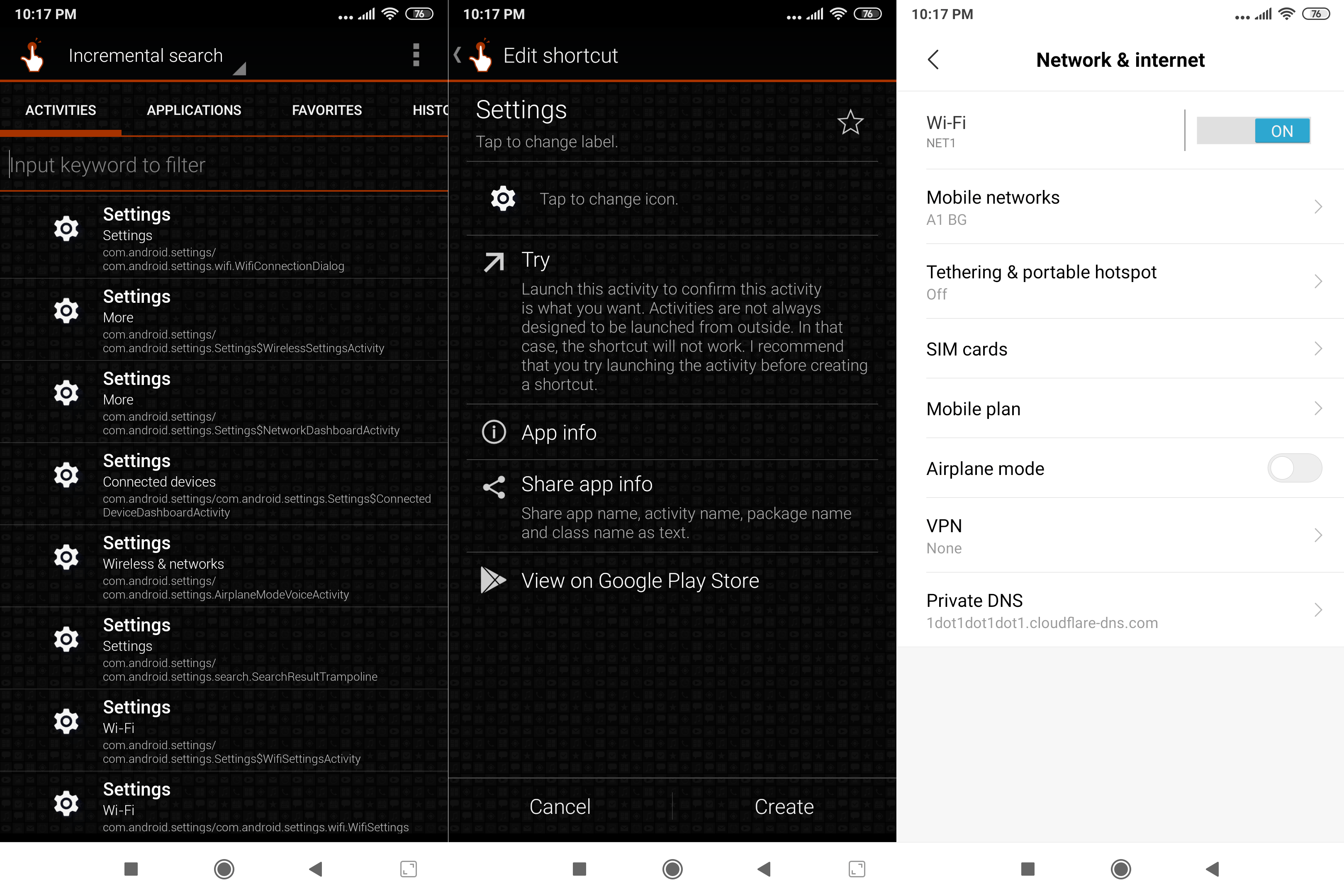
Enable DNS-over-TLS (for Android Pie and above)
In Android 9.0 (Pie) and above, not only can you encrypt your DNS traffic in Firefox Mobile, but for the entire operating system using DNS-over-TLS. On a stock Android handset (e.g. a Pixel or Android One device), navigate to Settings → Network & internet → Advanced → Private DNS.
Select the Private DNS provider hostname option, enter 1dot1dot1dot1.cloudflare-dns.com and hit Save. If your Android smartphone or tablet runs a skinned version from the device manufacturer, you can download an app called QuickShortcutMaker to access the Network & internet → Advanced menu.
Launch QuickShortcutMaker and in the Activities tab, scroll down to where Settings is listed and tap to expand it. Choose the option listed as Settings – More – com.android.settings/com.android.settings.Settings$NetworkDashboardActivity. Then tap Try, and you will see the Network & internet → Advanced menu where you can configure Private DNS.
Use a VPN when connected to public Wi-Fi hotspots
 A virtual private network (VPN) establishes a secure tunnel between your device and a VPN server, which relays the data you transmit between you and its final destination. Similar to the VPN gateways used by remote workers to connect back to their company’s internal corporate network, the traffic is completely encrypted and invisible to any onlookers.
A virtual private network (VPN) establishes a secure tunnel between your device and a VPN server, which relays the data you transmit between you and its final destination. Similar to the VPN gateways used by remote workers to connect back to their company’s internal corporate network, the traffic is completely encrypted and invisible to any onlookers.
Why use a VPN when connected to a public Wi-Fi hotspot? Well, Wi-Fi hotspots at cafes, airports, and even hotels tend to be insecure. Even if they are secured by a WPA/WPA2 preshared key, anybody who knows the Wi-Fi password can use it to intecept and decrypt the wireless packets from the other nodes. Regardless of whether the access point requires you to login with a captive portal (e.g. enter your last name and room number), as long as the network is not secured by WPA2 Enterprise/RADIUS with individual logins for each user, any transmitted data is visible to other users of the Wi-Fi network. Furthermore, many network administrators do not implement AP Isolation correctly, potentially allowing other users to discover your shared network folders and devices.
Especially at conferences or other popular locations, honeypots known as “Wi-Fi pineapples” are set up with a decoy network name (SSID) to trick unsuspecting users into connecting to it. If you transmit any data over a non-encrypted protocol such as HTTP, a rogue access point may be able to hijack the connection and replay session tokens to obtain unauthorized access to sensitive accounts. Also, compromised access points can be used to distribute malware in a “drive-by attack” that could install a keylogger, mine cryptocurrencies for the attacker, or force your device to become part of a botnet.
To protect you privacy and security before using public Wi-Fi, connect to a VPN that you set up yourself on a server that you control (in your home, office, or on a hosted server), or which belongs to a reputable, non-logging VPN service such as ProtonVPN.
Switch from Gmail to self-hosted email with Mailcow
Gmail is the most popular free email service in the world, but you pay with your privacy when you use it, especially without a G Suite subscription. Free Gmail accounts are ad-supported with Google robots that scan the content of your email messages, to serve you contextual ads. Also, if you use a free Gmail account, you have no way of controlling whether the emails are stored within Google’s US or EU infrastructure – paid G Suite accounts have the option to select this.
Either way, you’re at the mercy of Google to handle your email data according to its privacy policies – whether you use Gmail or G Suite. With our email inboxes straight at the center of our digital lives (e.g. password resets rely on email), there’s reason to be concerned. Some Gmail users have been locked out of their accounts without a way to contact a Google representative, because they were not a paying G Suite customer. They only recovered their accounts in the end because they knew somebody influential on social media, who could convince a Google employee to intervene.
Mailcow is a self-hosted alternative to hosted email providers such as G Suite or Office 365. It requires having your own domain name and configuring a server with the Mailcow stack, consisting of Postfix, Dovecot, and SOGo groupware. With your own domain, you have the option to migrate to any email server at anytime without losing your address, unlike relying on an Gmail.com or Outlook.com address.
With Mailcow you can create as many email aliases or inboxes as you like, without any restrictions. This is excellent for entrepreneurs, businesses, and organizations who want to project a more professional presence by having tailored email addresses.
The Mailcow data (inboxes and calendars) can be encrypted on the server that you manage, and you know exactly where it is stored, whether on-premises or with a cloud provider. Also, for the outbound email gateway that you use, you can choose one located in the EU so your personal data is protected by privacy laws such as the GDPR.
Switch from Dropbox, Google Drive, OneDrive to NextCloud
 Syncing your files to a cloud storage service can be a convenient way to access your files to stay productive and collaborate with team members from anywhere, but using commercial services such as Dropbox, Google Drive, or OneDrive comes with significant privacy ramifications. Some cloud storage providers, such as Amazon Cloud Drive, scan the contents of your cloud storage to calculate hashes for your files, and deduplicate them against identical files stored by other accounts. OneDrive has also been reported to trawl through the contents of customer cloud storage accounts, under the guise of finding illegal content the violates their Terms of Service. Wouldn’t you like to not be treated like a criminal, and host your own cloud storage in any environment of your choice? With NextCloud, That could be on-premises on a NAS in your office, or on a virtual server, with expandable object or block storage from a cloud provider.
Syncing your files to a cloud storage service can be a convenient way to access your files to stay productive and collaborate with team members from anywhere, but using commercial services such as Dropbox, Google Drive, or OneDrive comes with significant privacy ramifications. Some cloud storage providers, such as Amazon Cloud Drive, scan the contents of your cloud storage to calculate hashes for your files, and deduplicate them against identical files stored by other accounts. OneDrive has also been reported to trawl through the contents of customer cloud storage accounts, under the guise of finding illegal content the violates their Terms of Service. Wouldn’t you like to not be treated like a criminal, and host your own cloud storage in any environment of your choice? With NextCloud, That could be on-premises on a NAS in your office, or on a virtual server, with expandable object or block storage from a cloud provider.